Managed Network Detection and Response
Network security and visibility needs more than just logs
A managed Network Detection and Response (NDR) service can provide a level of visibility and security that can be difficult to maintain in-house, both in terms of availability and expertise. The LRQA Nettitude Managed NDR service can be utilised by organisations that have limited resources and expertise to assist with the provision, management, and monitoring of Network Detection and Response technologies, to provide the world-class capability to protect your environment.
LRQA Nettitude is an award-winning cybersecurity organisation with unparalleled capability in delivering managed security services. Through our global Managed Security Operations Centre (SOC) we deliver round-the-clock services that secure our clients and detect and respond to sophisticated cyber-threats, providing assurance that your organisation is protected.
What is Managed NDR?
NDR technologies continuously monitor an organisation’s network to detect cyber-threats, anomalous behaviour, or malicious traffic using non-signature-based tools and techniques that provide real-time continuous monitoring and detection, combined with response and analysis capabilities.
Advanced NDR solutions provide complete visibility across all users, devices, and technologies connected to the network providing coverage across end-users, data centres, and cloud environments.
Network traffic is continuously monitored when entering, exiting, and moving within the network for unprecedented visibility utilising behavioural analytics and machine learning to detect cyber-threats and anomalous behaviour. This data is captured in real-time and used to detect and model against known adversary tactics, techniques, and procedures providing a holistic contextual network-wide visibility.

The importance of network detection and response is recognised as a key pillar of the Gartner SOC visibility triad. A common misconception is that Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR) solutions sufficiently protect the enterprise environment. Yet, the widespread adoption of IoT, cloud computing, and digital transformation means that NDR is an increasingly important tool within the SOC visibility triad to combat sophisticated attackers.
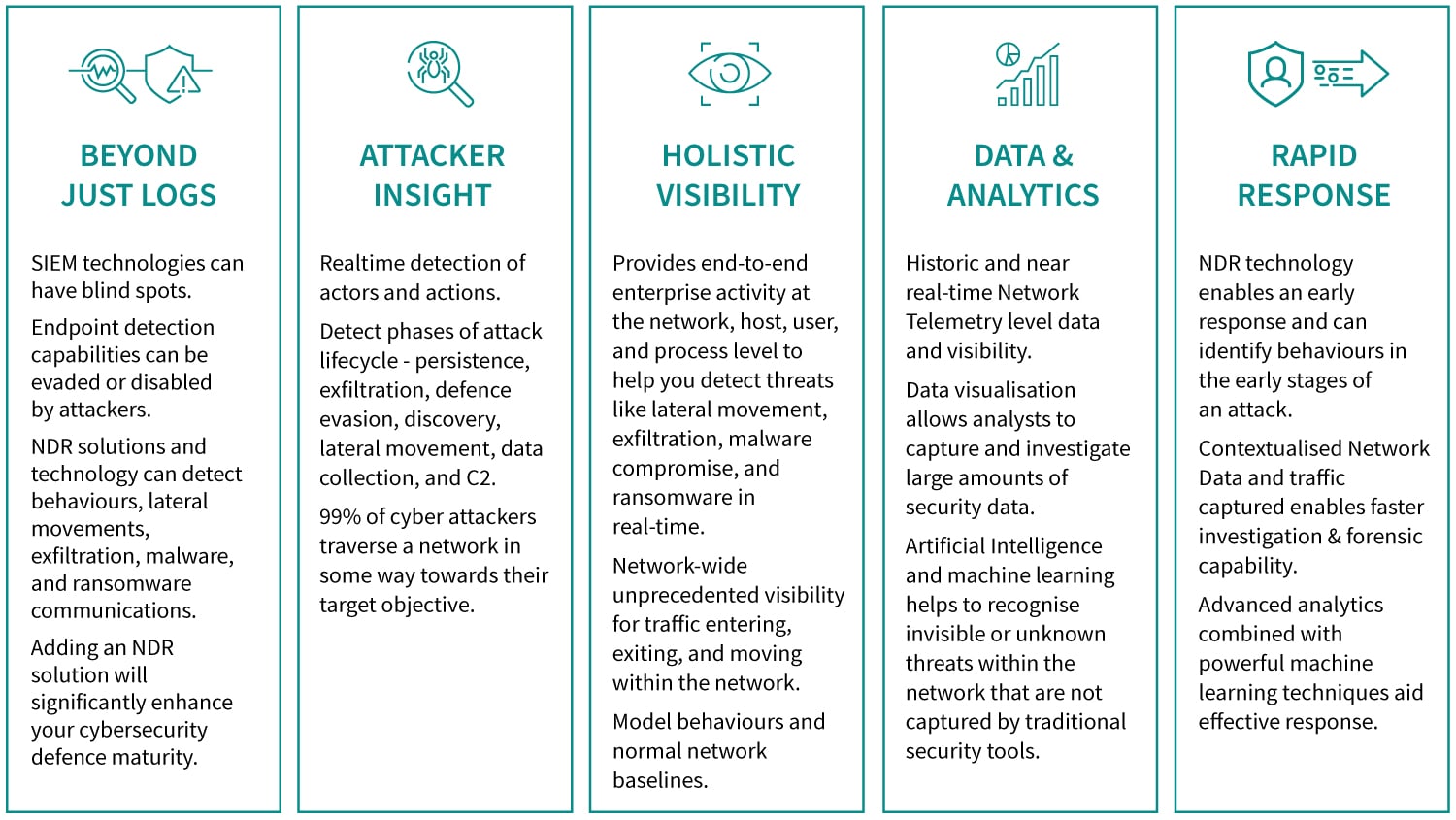
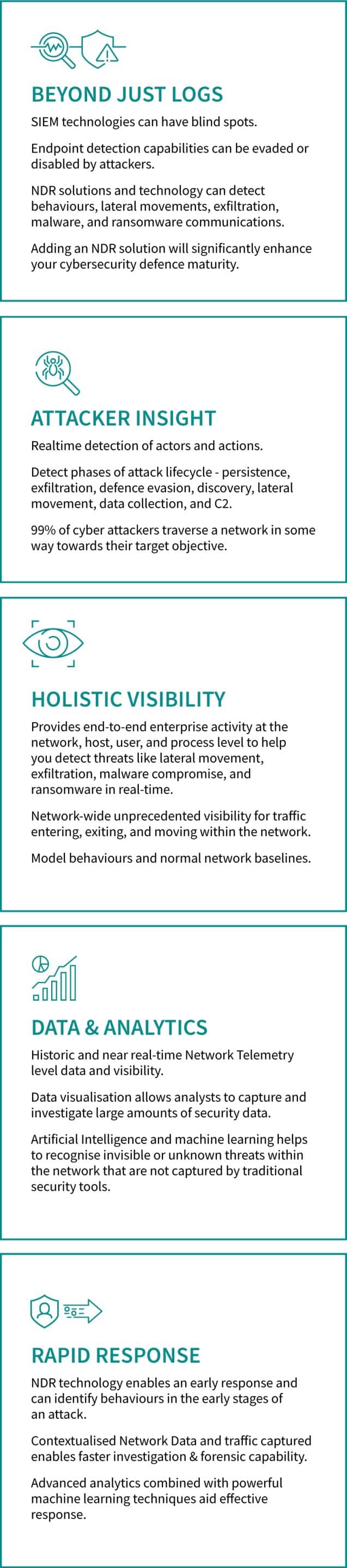
Benefits of Managed NDR
A common misconception is that SIEM and EDR tools will provide sufficient protection against cyber threats and attacks. These tools are a good start and form two corners of the SOC visibility triad. However, networks have become an increasingly valuable target with the widespread adoption of new technologies like cloud and IoT.
Adopting an NDR solution will significantly enhance your cybersecurity defensive stance whilst also ensuring your ability to defend against both sophisticated network attacks and highly organised threat actors.
Network Detection & Response Technology
Corelight
Corelight delivers the most powerful network visibility solutions for cybersecurity professionals. It helps them understand network traffic and defend their organisations more effectively.
Corelight solutions are built on the Zeek framework (formerly known as ‘Bro’), the powerful and widely-used open-source network analysis framework that generates actionable, real-time data for thousands of security teams worldwide.
Zeek data has become the gold standard for incident response, threat hunting, and forensics in large enterprises and government agencies worldwide.
Corelight makes a family of network sensors (both physical and virtual) at every scale, that takes the pain out of deploying open-source Zeek by adding integrations and capabilities large organisations need.
Corelight Sensors extract more than 400 data elements from network traffic in real-time, using a format chosen by incident responders, for incident responders. The Corelight Sensor is zero-maintenance and fine-tuned for enterprise performance at scale providing unrivalled network detection capability.
Managed NDR – Service Features
LRQA Nettitude’s managed Network Detection and Response service provides the most highly accredited expertise combined with Gartner Magic Quadrant leading security technology to deliver industry-leading protection for your organisation.
Our approach is proactive, and threat led; informed by our offensive and threat intelligence teams to shape our defensive stance and protect against the latest industry threats, providing in-depth unrivalled detection and alerting capability where it is needed most.

Protect your organisation with LRQA Nettitude’s award-winning cybersecurity services
Speak to one of our cybersecurity experts now…
Protect your organisation with LRQA Nettitude’s award-winning cybersecurity services
Speak to one of our cybersecurity experts now…