Develop a Cybersecurity Programme
Ensures your cyber strategy is equipped against evolving cyber threats
How do I prevent, withstand and recover from cyber incidents?
When it comes to cyber resilience, having a solid plan is key. This means not only having technical safeguards, such as firewalls and antivirus software but also regularly evaluating and updating your policies and procedures to ensure continual improvement and governance.
Implementing a cybersecurity programme to mitigate risk
A programme of this magnitude is highly complex and requires an organisational-wide effort to realise.
It is also important to have a disaster recovery plan in place to respond to any unforeseen cyber incidents quickly and effectively. This includes determining the appropriate steps to take and assigning clear roles and responsibilities to the response team.
By implementing these measures, your organisation can improve its overall cyber resilience and minimise potential disruptions to business operations.
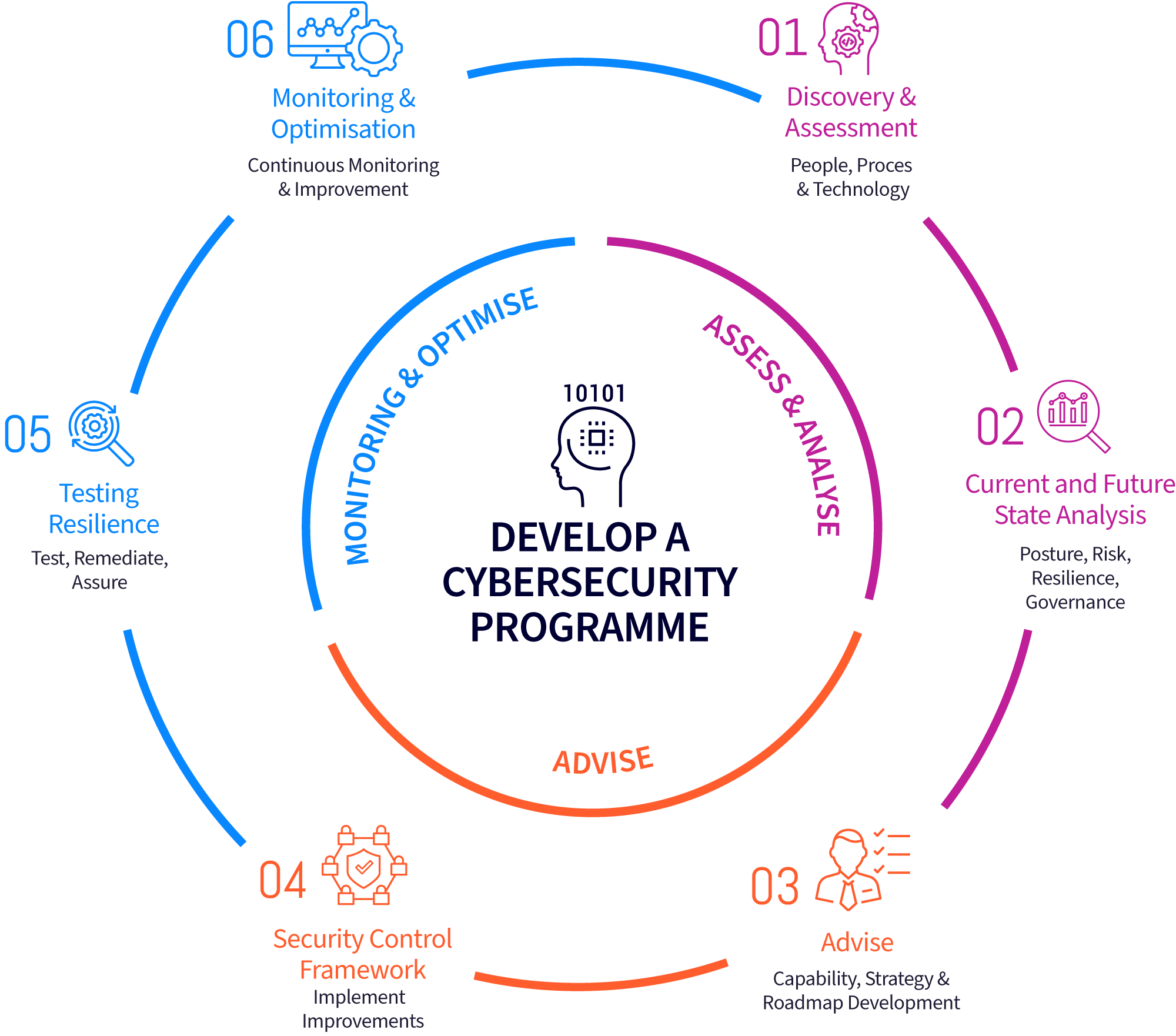
Package Approach
This package has three core phases and is a guided journey supported by focusing on technology, staff, and people.
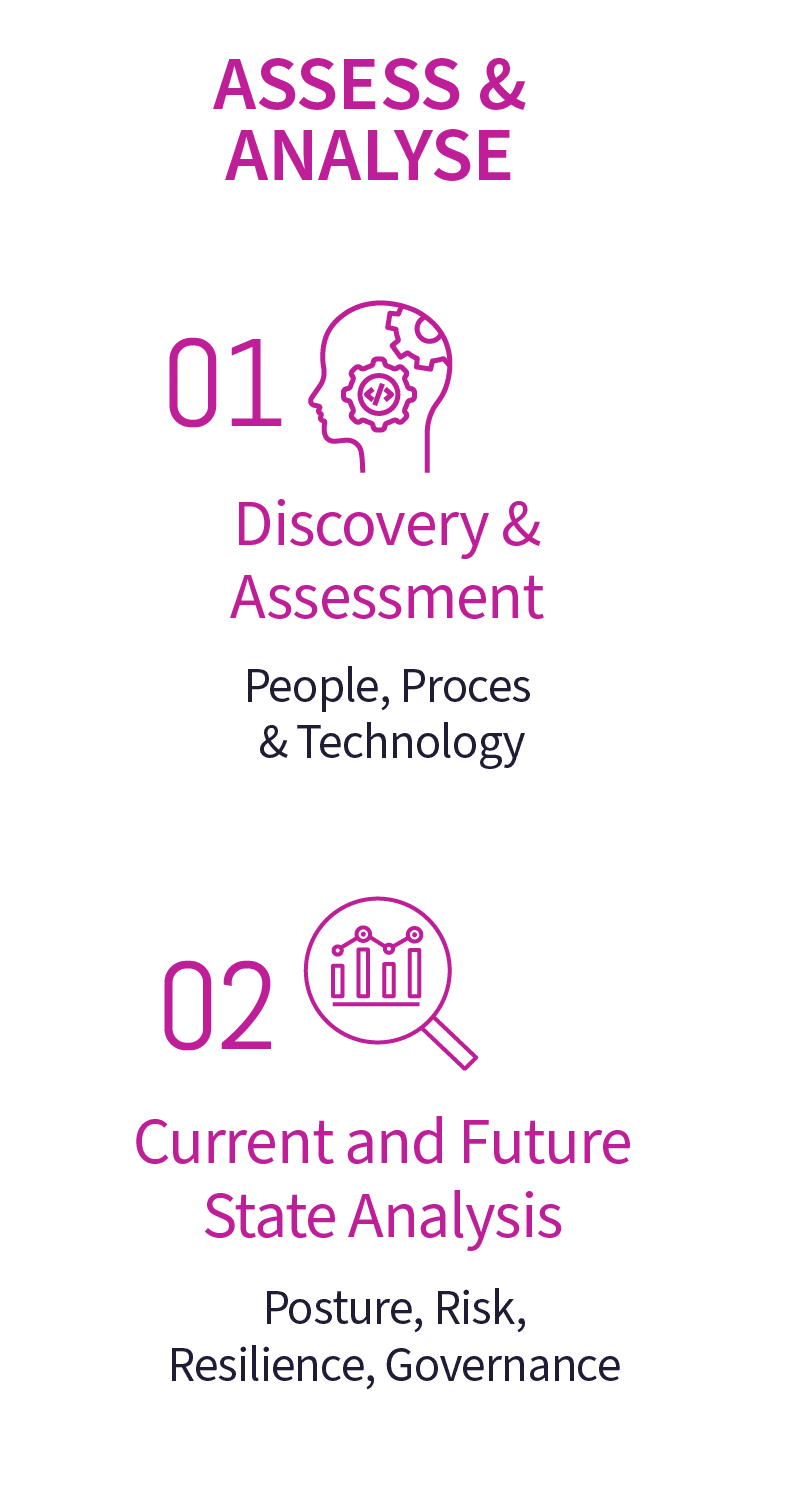
Assess & Analyse
• Discovery and assessment of your cyber posture, risks, and governance. Followed by analysing your strengths, weaknesses, and future desired state.
Advise
• Provides expert capability and guidance in the development of a cybersecurity programme incorporating plans, roadmaps, and objectives aligned to assessments and improvements needed.
Monitoring & Optimise
• Provision of services that support detection, protection, and response capability. End-user awareness training programs combined with technology-based simulation tests ensure a continually improving approach to maturity.
Choose our Develop a Cybersecurity Programme package
This package allows you to understand your current position and build a journey to increasing your cyber maturity posture organisation wide.

Baseline Package
• CISO Services
A LRQA Nettitude security expert who can provide strategic and tactical guidance to your organisation and help develop and execute a security program to ensure your organisation’s information and technologies are protected from all cyber threats.
LRQA Nettitude’s CISO services help drive your organisation’s vision, strategy, and implementation to ensure you meet your information security objectives.
• Cyber Strategy & Resilience Assessment
• Policy & Documentation Assessment
Quickly understand your organisation’s security posture to take risk-based decisions on improvement planning and budget and resource allocation.
Conducted through workshops, this service asks insightful and valuable questions that will enable a clear view of your cybersecurity needs and identifies any gaps and areas for improvement. Benchmarked against industry standards this assessment provides an external review and assurance of your organisation’s cyber maturity.
• Asset & Vulnerability Assessment
• Risk Monitoring & Reporting
• Security Awareness Training
• Penetration Testing
A penetration test is an attempt to evaluate the security of your IT infrastructure through the safe exploitation of vulnerabilities via certified professionals.
LRQA Nettitude specialises in the delivery of rigorous and strenuous security testing and provides you with a report on how attackers can exploit weaknesses in your infrastructure, networks, people, and processes.
• Managed Vulnerability Scanning
Our Managed Vulnerability Scanning Service deploys a leading cloud-based vulnerability scanning and management technology to be able to identify, investigate, prioritise, mitigate, and respond to vulnerabilities within your environment and attack surface.
Understanding your risks as the number of vulnerabilities increases is critical in the current threat landscape. Managed Vulnerability Scanning is a fundamental component of any security testing programme for identifying existing or new vulnerabilities and misconfigurations across your systems.
LRQA Nettitude MVSS services have multiple customisable options tailored to fit your organisation that aid cyber maturity and risk-based methodologies to help you remediate and stay on top of critical issues and vulnerabilities that could leave you exposed.
General Enquiry.
Explore More Cyber Packages…
Ransomware & Malware
How safe is your organisation from a ransomware threat? Ensure you are always prepared for a ransomware or malware attack with this package.
Learn More…
Cyber Breach Readiness
Is your organisation prepared for a cyber breach? This package prepares your organisation and ensures you can respond to a breach.
Learn More…
Supplier & Third-Party Risk Management
Can you trust your supplier’s and third-parties cybersecurity? Select this package for complete assurance, governance, and risk management of your supply chain.
Learn More…
Penetration Testing Remediation
Penetration Tests have identified your weaknesses, but do you know how to remediate vulnerabilities? Select this package to ensure remediation is fully executed.
Learn More…
New Technology Cyber Risks
Concerned that moving to new technology will increase cyber risks? Choose this package for assurance that new technology is secured and protected by experts.
Learn More…
Technical Legacy Debt
Do you know legacy software systems can expose you to cyber threats? Ensure your systems are safe with this package to manage and secure legacy systems.
Learn More…
Develop a Cybersecurity Programme
Ensures your cyber strategy is equipped against evolving cyber threats
How do I prevent, withstand, and recover from cyber incidents?
When it comes to cyber resilience, having a solid plan is key.
This means not only having technical safeguards, such as firewalls and antivirus software but also regularly evaluating and updating your policies and procedures to ensure continual improvement and governance.
Implementing a cybersecurity programme to mitigate risk
A programme of this magnitude is highly complex and requires an organisational-wide effort to realise.
It is also important to have a disaster recovery plan in place to respond to any unforeseen cyber incidents quickly and effectively.
This includes determining the appropriate steps to take and assigning clear roles and responsibilities to the response team.
By implementing these measures, your organisation can improve its overall cyber resilience and minimise potential disruptions to business operations.
Package Approach
This package has three core phases and is a guided journey supported by focusing on technology, staff, and people.
Assess & Analyse
Discovery and assessment of your cyber posture, risks, and governance. Followed by analysing your strengths, weaknesses, and future desired state.
Advise
Provides expert capability and guidance in the development of a cybersecurity programme incorporating plans, roadmaps, and objectives aligned to assessments and improvements needed.

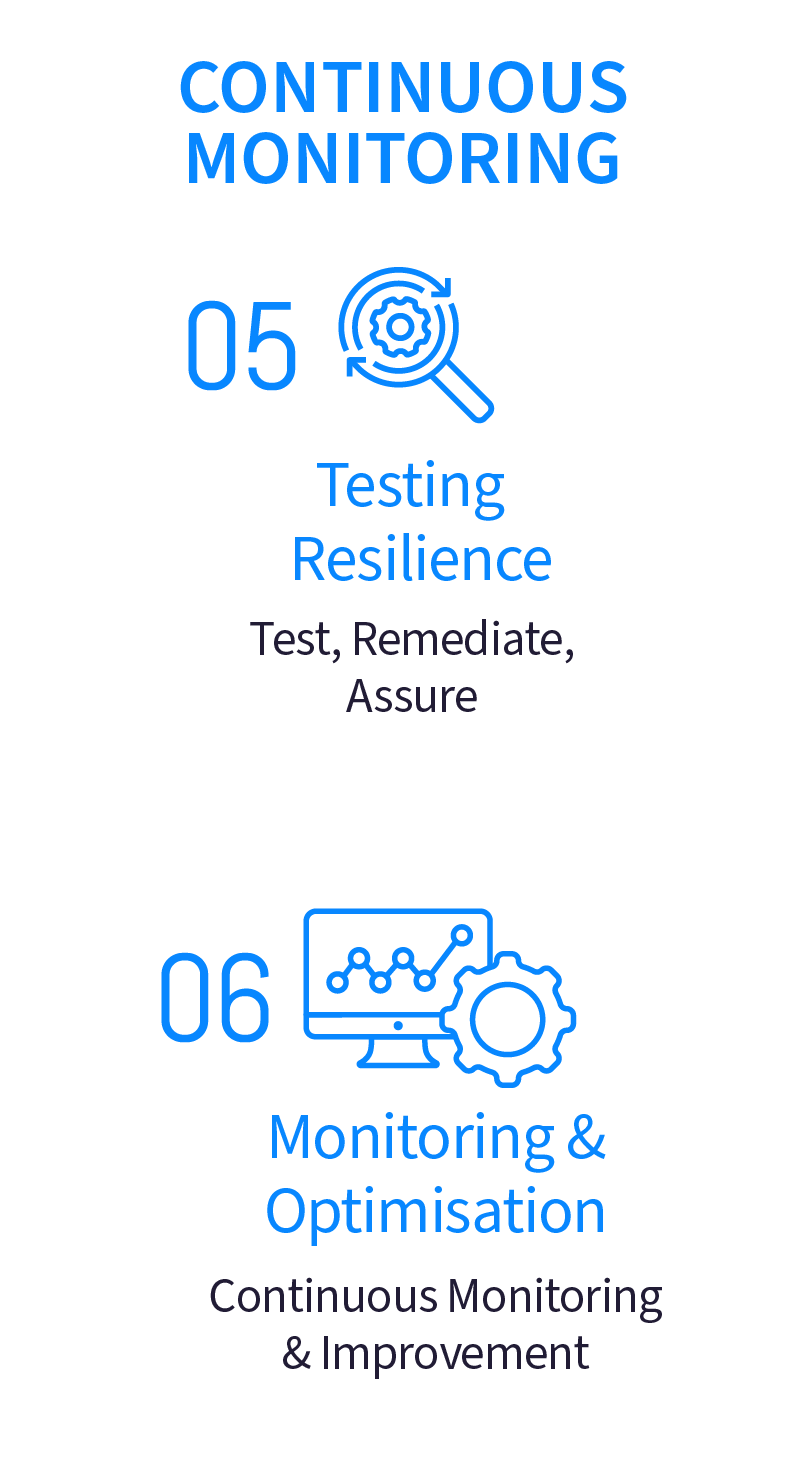
Continuous Monitoring
Provision of services that support detection, protection, and response capability. End-user awareness training programs combined with technology-based simulation tests ensure a continually improving approach to maturity.
Choose our Develop a Cybersecurity Programme package
This package allows you to understand your current position and build a journey to increasing your cyber maturity posture organisation wide.

Baseline Package
• CISO Services
A LRQA Nettitude security expert who can provide strategic and tactical guidance to your organisation and help develop and execute a security program to ensure your organisation’s information and technologies are protected from all cyber threats.
LRQA Nettitude’s CISO services help drive your organisation’s vision, strategy, and implementation to ensure you meet your information security objectives.
• Cyber Strategy & Resilience Assessment
• Policy & Documentation Assessment
Quickly understand your organisation’s security posture to take risk-based decisions on improvement planning and budget and resource allocation.
Conducted through workshops, this service asks insightful and valuable questions that will enable a clear view of your cybersecurity needs and identifies any gaps and areas for improvement. Benchmarked against industry standards this assessment provides an external review and assurance of your organisation’s cyber maturity.
• Asset & Vulnerability Assessment
• Risk Monitoring & Reporting
• Security Awareness Training
• Penetration Testing
A penetration test is an attempt to evaluate the security of your IT infrastructure through the safe exploitation of vulnerabilities via certified professionals.
LRQA Nettitude specialises in the delivery of rigorous and strenuous security testing and provides you with a report on how attackers can exploit weaknesses in your infrastructure, networks, people, and processes.
• Managed Vulnerability Scanning
Our Managed Vulnerability Scanning Service deploys a leading cloud-based vulnerability scanning and management technology to be able to identify, investigate, prioritise, mitigate, and respond to vulnerabilities within your environment and attack surface.
Understanding your risks as the number of vulnerabilities increases is critical in the current threat landscape. Managed Vulnerability Scanning is a fundamental component of any security testing programme for identifying existing or new vulnerabilities and misconfigurations across your systems.
LRQA Nettitude MVSS services have multiple customisable options tailored to fit your organisation that aid cyber maturity and risk-based methodologies to help you remediate and stay on top of critical issues and vulnerabilities that could leave you exposed.
General Enquiry.
Explore More Cyber Packages…
Ransomware & Malware
How safe is your organisation from a ransomware threat? Ensure you are always prepared for a ransomware or malware attack with this package.
Learn More…
Cyber Breach Readiness
Is your organisation prepared for a cyber breach? This package prepares your organisation and ensures you can respond to a breach.
Learn More…
Supplier & Third-Party Risk Management
Can you trust your supplier’s and third-parties cybersecurity? Select this package for complete assurance, governance, and risk management of your supply chain.
Learn More…

Employee Security & Training
Concerned about how to protect against threats that target employees? This package will secure and train employees while monitoring the threats they face.
Learn More…
Penetration Testing Remediation
Penetration Tests have identified your weaknesses, but do you know how to remediate vulnerabilities? Select this package to ensure remediation is fully executed.
Learn More…
New Technology Cyber Risks
Concerned that moving to new technology will increase cyber risks? Choose this package for assurance that new technology is secured and protected by experts.
Learn More…
Technical Legacy Debt
Do you know legacy software systems can expose you to cyber threats? Ensure your systems are safe with this package to manage and secure legacy systems.
Learn More…
Explore More Cyber Packages…
Ransomware & Malware
How safe is your organisation from a ransomware threat? Ensure you are always prepared for a ransomware or malware attack with this package.
Learn More…
Cyber Breach Readiness
Is your organisation prepared for a cyber breach? This package prepares your organisation and ensures you can respond to a breach.
Learn More…
Supplier & Third-Party Risk Management
Can you trust your supplier’s and third-parties cybersecurity? Select this package for complete assurance, governance, and risk management of your supply chain.
Learn More…

Employee Security &
Training
Concerned about how to protect against threats that target employees? This package will secure and train employees while monitoring the threats they face.
Learn More…
Penetration Testing Remediation
Penetration Tests have identified your weaknesses, but do you know how to remediate vulnerabilities? Select this package to ensure remediation is fully executed.
Learn More…
New Technology
Cyber Risks
Concerned that moving to new technology will increase cyber risks? Choose this package for assurance that new technology is secured and protected by experts.
Learn More…
Technical Legacy
Debt
Do you know legacy software systems can expose you to cyber threats? Ensure your systems are safe with this package to manage and secure legacy systems.
Learn More…




